The programmatic ecosystem is bleeding out. Nobody cares. Agencies buy the inventory, publishers cash the checks, and verification vendors collect their tax. Look under the hood of your premium traffic. It is a graveyard of automated scripts. We are fighting advanced botnets with toys.
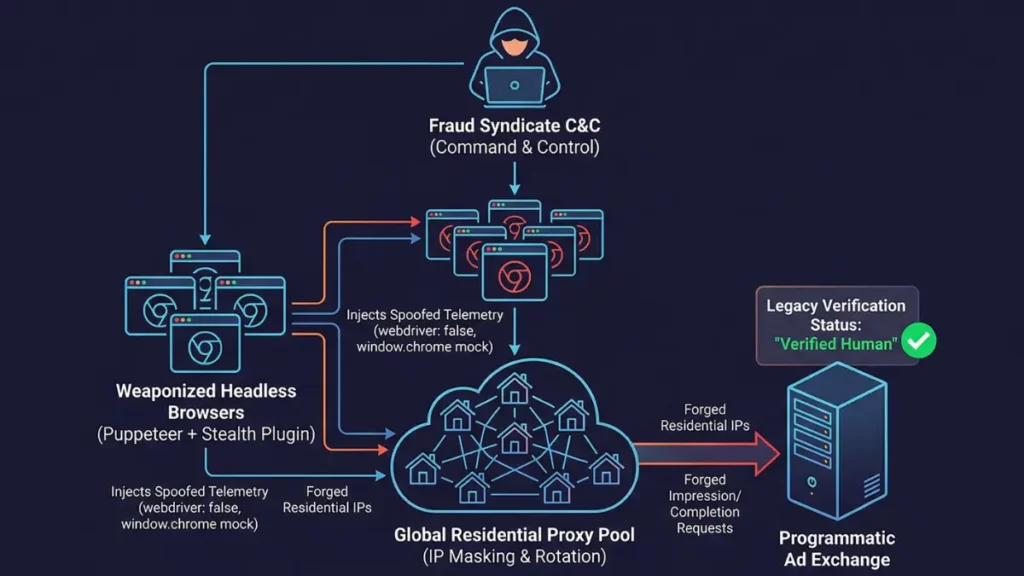
The Illusion of “Verified Human” Traffic
Your verification vendor is lying to you. They sell a dashboard showing 99% viewability and pristine brand safety. It is a fabricated reality.
Basic JavaScript fingerprinting is functionally dead. The days of catching raw cURL requests and lazy Python scrapers ended years ago. Modern arbitrage rings do not just scrape text. They render the entire payload.
Puppeteer is no longer a QA tool. It is the engine of distributed ad fraud. Bot operators use headless Chromium to execute complex DOM mutations, trigger third-party pixels, and generate synthetic video completions at scale.
Vanilla headless Chrome is loud. It leaks its automated nature across the network stack. But add a weaponized stealth plugin, and the telemetry changes entirely. The bot becomes a ghost.
Anatomy of the Exploit: The puppeteer-extra-plugin-stealth
The objective is simple. Lie to the DOM.
This plugin exists to falsify the browser’s execution environment. It takes a loud, easily detectable headless Chromium instance and weaponizes it for arbitrage. It is the gold standard for bypassing basic ad fraud checks.
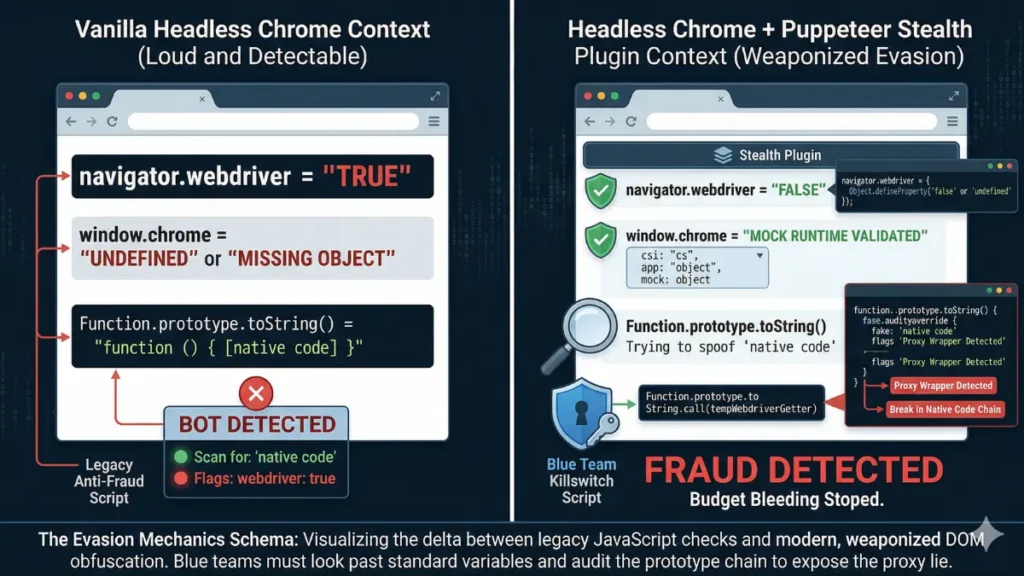
Fingerprint 1: The navigator.webdriver Patch
Vanilla headless Chrome screams its identity. It broadcasts navigator.webdriver: true across the execution environment. This is a fatal flaw for botnets.
The stealth plugin intercepts this object entirely. It uses JavaScript’s Object.defineProperty to rewrite reality.
- Target: The
navigatorobject prototype. - Execution: Overrides the
webdrivergetter to force afalseorundefinedreturn. - Result: Lazy vendor scripts read the falsified DOM. They rubber-stamp the session as human.
Fingerprint 2: Spoofing the window.chrome Runtime
Legitimate Chrome browsers possess a specific, complex runtime object. Headless environments do not. They are stripped down for speed.
DOM-scanning anti-bot tags look for this delta. If window.chrome is missing, the traffic gets flagged. The exploit targets this assumption directly.
The stealth payload injects mock properties directly into the DOM. It builds fake window.chrome.csi and window.chrome.app structures. The bot meticulously constructs a counterfeit runtime environment. The verification vendor’s JavaScript checks the box, charges a CPM fee, and moves on.
The iframe.contentWindow Evasion
Smart blue teams know the DOM is a warzone. They do not trust the parent window. They build traps.
The trap is a dynamically created iframe. When a new iframe is appended to the DOM, it generates a fresh, clean execution context. It strips away the parent page’s tampered variables and exposes the underlying browser environment. The webdriver flag usually reappears here.
Fraudsters adapted immediately. The stealth plugin counters this by hooking directly into the iframe creation process itself.
It intercepts the element before it fully attaches to the DOM. It injects its evasion scripts directly into the contentWindow.
- Monitor: Wraps
document.createElement('iframe')with a proxy function. - Intercept: Modifies the
srcdocorcontentWindowproperties upon initialization. - Execute: Injects the stealth payload inside the iframe before the parent page’s detection scripts are allowed to execute.
The trap is disarmed before it even snaps shut. The ad verification tag loads inside the iframe, scans the environment, and sees the exact same spoofed telemetry. The exploit holds. The budget bleeds.
Field Data: Synthetic Traffic at Scale
We saw this execution live during a recent Q4 programmatic video campaign. It was a bloodbath.
The vendor dashboard showed a sudden 350% spike in video completion rates across mid-tail publisher domains. The traffic was originating exclusively from residential IP blocks. It looked perfect on paper.
It was entirely synthetic. The botnet leveraged an architecture heavily mimicking the 3ve operation. They hijacked legitimate residential proxies to mask the Puppeteer endpoints.
The anomaly was buried in the network telemetry. Human interactions are messy. This traffic was not.
- Latency Profile: Despite routing through residential nodes in the Midwest, interaction delays sat perfectly at 12ms. Every single time.
- Interaction Scores: The synthetic leads were passing Google’s automated checks with 0.9 reCAPTCHA v3 scores.
- Fingerprint: The DOM profiles matched the exact stealth Puppeteer signatures. Spoofed
navigator.webdriver, patchedwindow.chrome, and absolutely zero WebGL entropy.
[THREAT INTEL: SYNTHETIC VIDEO COMPLETION EVENT]
timestamp: 2025-11-24T02:14:11.000Z
ip_asn: AS7018 (AT&T Services, Inc.) - [RESIDENTIAL MASK]
interaction_latency: 12.004ms
recaptcha_v3_score: 0.9
dom_entropy: {
"navigator.webdriver": "undefined (Tampered)",
"window.chrome.csi": "Present (Spoofed)",
"webgl_unmasked_vendor": "Google Inc. (Default Headless)",
"mouse_trajectory_variance": 0.0000001
}
// ACTION: DROP BID & BLACKLIST IPDetecting Prototype Tampering
You cannot trust the DOM. If a bot controls the execution environment, it controls the truth. Vendors relying on simple property checks are getting robbed blindly.
We do not look for the webdriver flag. We look for the lie.
When the stealth plugin overrides native browser functions to hide itself, it uses proxy wrappers. Native JavaScript functions return function () { [native code] } when you call .toString() on them. The stealth plugin tries to fake this, but it leaves a forensic trail in the prototype chain.
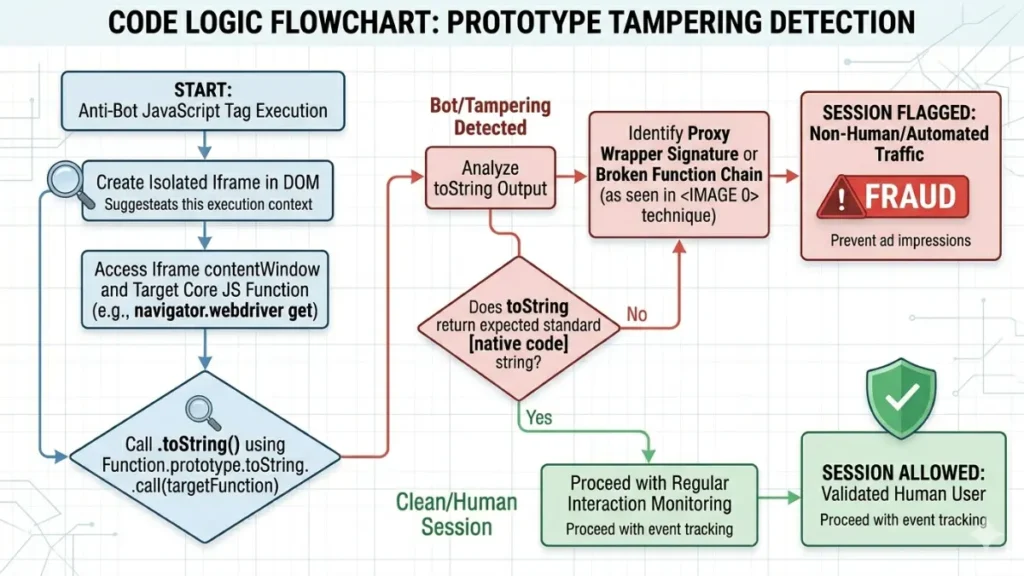
Deploy this script. It inspects the prototype chain directly to catch the tampering.
The script creates a controlled iframe and bypasses the getter overrides. It forces the function to reveal its true string representation using Function.prototype.toString.call().
If the bot is running the stealth plugin, the execution chain breaks. The proxy wrapper is exposed.
The session is flagged, the bid is dropped, and the budget is saved. Stop relying on vendor dashboards. Audit your own logs.